Learn the commands to install and configure Ansible on Rocky Linux 8 or CentOS to automate the process of installing and configuring multiple Linux servers simultaneously.
If you have to manage multiple Linux servers then manually configuring and installing software on each of them is not only a time-consuming but also a labor-intensive task. Thus, Automation or orchestration is used in such environments.
There are already well know applications available to perform orchestration for server systems/data centers such as Ansible, Puppet, Chef, and a few others. Well, here we learn about Ansible and how to use it to centrally manage multiple servers for installing various packages; code deployment, network configuration, cloud management, and much more.
Ansible is an open-source project sponsored by RedHat, thus if somebody wants, support and a graphical interface for Ansible they can go for the paid additions Tower’offered by RedHat. One of the biggest advantages of Ansible is the ready-made “playbooks” that are made available on GitHub.
Ansible works in the push procedure and does not require any further installation on individual systems besides SSH and Python. Compared to Chef and Puppet, the management and use of Ansible are easier,
Steps to install Ansible on Rocky Linux 8
The steps and commands given here to install Ansible are also applicable for AlmaLinux and CentOS 8.
1. Run system update
On your Rocky Linux 8 server or desktop, go to the command terminal and first run the system update command where you are planning to set up Ansible.
sudo dnf update
2. Enable EPEL repository
Install Ansible on Rocky Linux 8 is available in the EPEL repository while other dependencies can be resolved and installed through default repos- baseos and appstream. Thus, enable EPEL on your Linux using the default package manager-
sudo dnf install epel-release
3. Install Ansible on Rocky Linux
Now, run the main Ansible command that will fetch and install its packages along with other requirements such as Python.
sudo dnf install ansible
Accept the request to install packages and GPG key by typing – Y and hit
4. Check the Ansible version on Rocky Linux
Let’s check the installer version of Ansible on our system using-
ansible --version
Something this will be the result if everything is working fine-
ansible 2.9.21 config file = /etc/ansible/ansible.cfg configured module search path = ['/home/h2s/.ansible/plugins/modules', '/usr/share/ansible/plugins/modules'] ansible python module location = /usr/lib/python3.6/site-packages/ansible executable location = /usr/bin/ansible python version = 3.6.8 (default, Apr 12 2021, 07:42:28) [GCC 8.3.1 20191121 (Red Hat 8.3.1-5)] [h2s@localhost ~]$
5. Configure Target Servers
The servers which you want to manage using Ansible must have SSH installed and port 22 opened in the firewall to access them from other systems such as the one installed with Ansible.
Here we are using Ubuntu, Debian, and CentOS as servers that we will use to configure using Ansible. Thus, to install the SSH server and open port 22 on them, you can use these commands.
For Ubuntu & Debian servers-
sudo apt install openssh-server sudo systemctl enable ssh
to allow port 22 in the firewall-
sudo ufw allow 22
For RHEL or CentOS
sudo dnf install openssh-server sudo systemctl enable sshd
Allow 22 in firewall-
sudo firewall-cmd --zone=public --permanent --add-port=22/tcp
So, here to perform this tutorial we have three servers Ubuntu, Debian, and CentOS, here are the IP addresses in our case.
- Ubuntu – 192.168.189.172
- CentOS – 192.168.0.102
- Debian – 192.168.0.104
6. Generate SSH Keys on Ansible installed Rocky Linux
To install packages or perform some deployment on a remote target server, create a pair of SSH keys on localhost and then push them on each remote server so that we can manage them using SSH.
Simply type and hit the Enter key multiple times until the generation of keys is not done.-
ssh-keygen
7. Copy SSH keys to Remote or Target servers
Now, push the generated key on Rocky Linux to the remote servers that you want to configure or manage. You should know the user name of the remote server or use the default root user.
Note: Replace h2s with remote servers’ sudo users or use the default root. Also, replace the Ip-address with your server’s.
ssh-copy-id [email protected] ssh-copy-id [email protected] ssh-copy-id [email protected]
Now, on each server run the below command, so that we can run commands with sudo on them using Ansible but without entering a password.
echo "$(whoami) ALL=(ALL) NOPASSWD:ALL" | sudo tee /etc/sudoers.d/$(whoami)
8. Create Inventory File for Remote Hosts
In Ansible, we create a file where we will define all the remote hosts or target systems that we want to manage. We can also create a group of hosts, for example, one group is a Web server that only contains a remote system running some web servers such as Apache, and the other can be a group of Mysql running a database server and so on. The Inventory file is also important because using it the command, modules, and tasks in a playbook will operate.
So, as here in this tutorial we have three remote servers, let’s add them to the Ansible host file.
sudo dnf install nano -y
sudo nano /etc/ansible/hosts
If you don’t want to create any group then simply paste your remote server Ip-address or domain name there in the file, whereas for creating a group you have to specify that before adding Ip-addresses. You can edit the default Ansible inventory file values that would already have some examples or add your own at the end of the file.
Here I am adding two servers for a host group identified by web servers and one server will define as an individual.
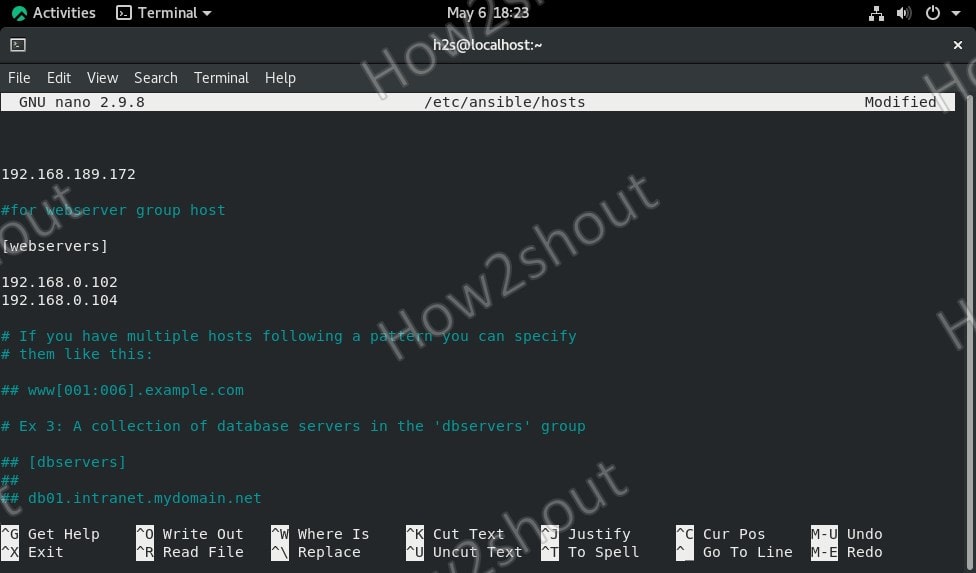
In the screenshot, you can see-
192.168.189.172
It is an ungroup server
whereas
[webservers] 192.168.0.102 192.168.0.104
are in a group called webservers. The benefit of creating a group is, we can issue one command to a whole set of servers defined in that particular group of hosts. For example, I can install an apache server on all remote servers added in a group called webservers simultaneously. In the same way, you can define database groups and others.
Note- Inventory with custom SSH port
If you are using some server not with the default 22 SSH port, for example, a server running on Docker then we can also define that with the Ip-address. Example-
192.168.0.104 ansible_user=remote-server-username ansible_port=49153
⇒In the above command replace the IP address, remote-server-username, and port number and add it to the inventory file.
To save the file just press Ctrl+X, Type-Y, and hit the Enter key.
9. Ping All added Remote servers
As we have created the inventory file successfully, let’s check whether our Ansible could ping all the added servers or not, for that-
To ping a group of hosts-
ansible -m ping group-name
example– ansible -m ping web-servers
To ping a single server
ansible -m ping ip-address
example– ansible -m ping 192.168.189.172
To ping all.
ansible -m ping all
10. Common Ansible commands to install packages or retrieve info from remote servers
Now, let’s say you want to install an Apache web server on one group of servers you have defined in the Inventory file. As here we already named one webserver, thus we use that, you can use whatever name you have given to your group of servers.
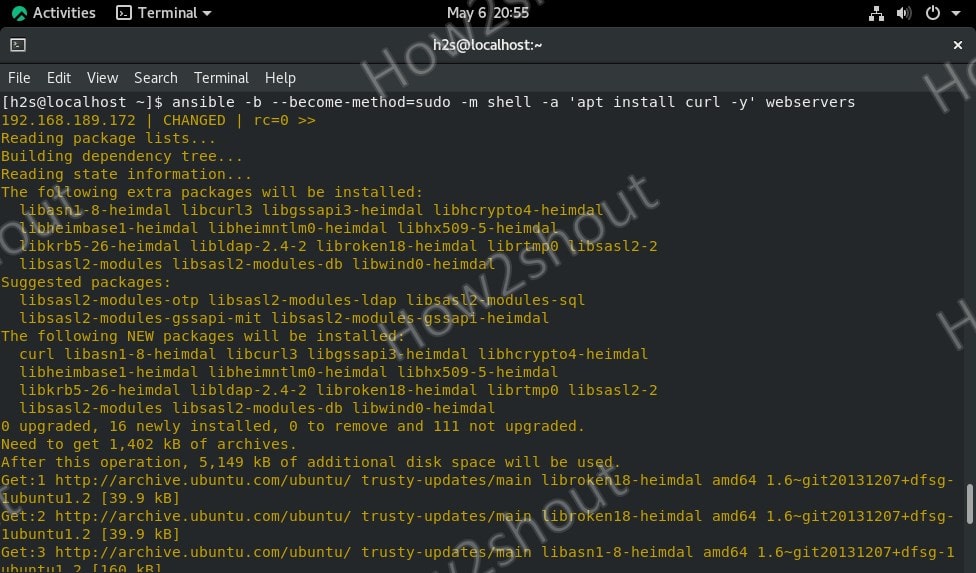
Command syntax
ansible -b --become-method=sudo -m shell -a 'command to execute' webservers
For example, running the update and installing the apache server on remote Debian and Ubuntu systems simultaneously.
ansible -b --become-method=sudo -m shell -a 'apt update' webservers
Installing Apache
ansible -b --become-method=sudo -m shell -a 'apt install -y apache2' webservers
To run the same above command for all defined remote PCs run-
ansible -b --become-method=sudo -m shell -a 'apt install -y apache2 ' all
For ungroup hosts, you can use their IP addresses, for example-
ansible -b --become-method=sudo -m shell -a 'apt install -y apache2' 192.168.0.104
You can also use other commands that don’t require sudo such as for checking uptime-
ansible -m command -a "uptime" group-name/ip-adress
The same above command can be used for other purposes, just replace uptime with the command that you want to execute on a remote server and also change group-name/IP-address.
For more information refer to the official Documentation.